Strengthening the Shield: Cybersecurity Strategies for SMEs




Interesting research: “Teams of LLM Agents can Exploit Zero-Day Vulnerabilities.”
Abstract: LLM agents have become increasingly sophisticated, especially in the realm of cybersecurity. Researchers have shown that LLM agents can exploit real-world vulnerabilities when given a description of the vulnerability and toy capture-the-flag problems. However, these agents still perform poorly on real-world vulnerabilities that are unknown to the agent ahead of time (zero-day vulnerabilities).
In this work, we show that teams of LLM agents can exploit real-world, zero-day vulnerabilities. Prior agents struggle with exploring many different vulnerabilities and long-range planning when used alone. To resolve this, we introduce HPTSA, a system of agents with a planning agent that can launch subagents. The planning agent explores the system and determines which subagents to call, resolving long-term planning issues when trying different vulnerabilities. We construct a benchmark of 15 real-world vulnerabilities and show that our team of agents improve over prior work by up to 4.5×...
The post Using LLMs to Exploit Vulnerabilities appeared first on Security Boulevard.
Interesting research: “Teams of LLM Agents can Exploit Zero-Day Vulnerabilities.”
Abstract: LLM agents have become increasingly sophisticated, especially in the realm of cybersecurity. Researchers have shown that LLM agents can exploit real-world vulnerabilities when given a description of the vulnerability and toy capture-the-flag problems. However, these agents still perform poorly on real-world vulnerabilities that are unknown to the agent ahead of time (zero-day vulnerabilities).
In this work, we show that teams of LLM agents can exploit real-world, zero-day vulnerabilities. Prior agents struggle with exploring many different vulnerabilities and long-range planning when used alone. To resolve this, we introduce HPTSA, a system of agents with a planning agent that can launch subagents. The planning agent explores the system and determines which subagents to call, resolving long-term planning issues when trying different vulnerabilities. We construct a benchmark of 15 real-world vulnerabilities and show that our team of agents improve over prior work by up to 4.5×.
The LLMs aren’t finding new vulnerabilities. They’re exploiting zero-days—which means they are not trained on them—in new ways. So think about this sort of thing combined with another AI that finds new vulnerabilities in code.
These kinds of developments are important to follow, as they are part of the puzzle of a fully autonomous AI cyberattack agent. I talk about this sort of thing more here.

“Most notably he is believed to be a key component of the MGM ransomware attack, and is believed to be associated with several other high profile ransomware attacks performed by Scattered Spider.” - vx-undergroundThe initial access vector in the attack on MGM included targeting of a help desk executive with social engineering tactics. Mandiant in its latest report found Scattered Spider aka UNC3944 using the same modus operandi, and although no victim names were stated, it now suggests the possible linkage between them. *Update (June 17 5:45 AM EST): Added details on the 22-year old young cyber scammer's identity and possible links to Scattered Spider group.

 Source: Dark Web[/caption]
The cyberattack on Unifi TV was aimed at disrupting the operation of the organization and highlighted the importance of robust cybersecurity measures in safeguarding critical digital infrastructure. Despite claims by the threat actor that the Unifi TV website was down, the web pages seem to be operational at the moment and don’t show any immediate sign of the cyberattack.
The impact of the cyberattack extends beyond Unifi TV, affecting not only the telecommunications industry but also posing a threat to Malaysia's digital ecosystem as a whole. With the country witnessing over 3,000 cyber attacks daily, according to Defence Minister Datuk Seri Mohamed Khaled Nordin, the cyberattacks on Malaysia highlights the growing nature of ransomware groups and hacktivist collectives targeting the nation.
Source: Dark Web[/caption]
The cyberattack on Unifi TV was aimed at disrupting the operation of the organization and highlighted the importance of robust cybersecurity measures in safeguarding critical digital infrastructure. Despite claims by the threat actor that the Unifi TV website was down, the web pages seem to be operational at the moment and don’t show any immediate sign of the cyberattack.
The impact of the cyberattack extends beyond Unifi TV, affecting not only the telecommunications industry but also posing a threat to Malaysia's digital ecosystem as a whole. With the country witnessing over 3,000 cyber attacks daily, according to Defence Minister Datuk Seri Mohamed Khaled Nordin, the cyberattacks on Malaysia highlights the growing nature of ransomware groups and hacktivist collectives targeting the nation.
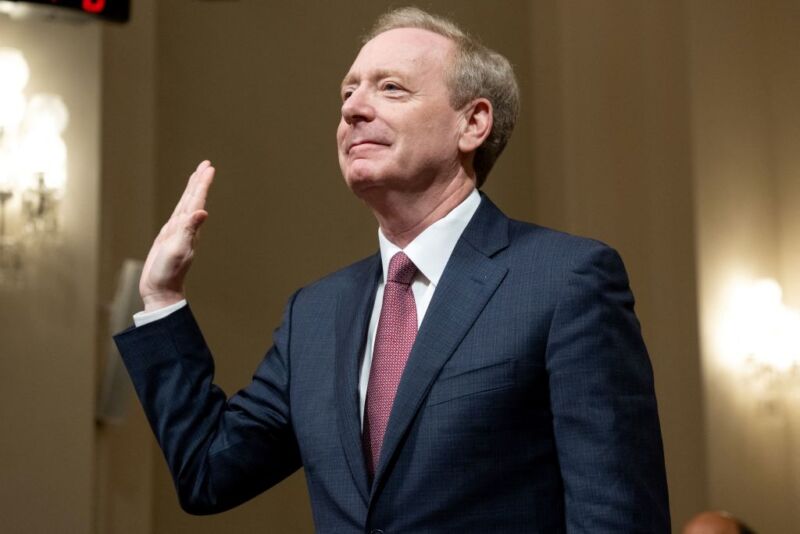
Enlarge / Brad Smith, vice chairman and president of Microsoft, is sworn in before testifying about Microsoft's cybersecurity work during a House Committee on Homeland Security hearing on Capitol Hill in Washington, DC, on June 13, 2024. (credit: SAUL LOEB / Contributor | AFP)
Microsoft is pivoting its company culture to make security a top priority, President Brad Smith testified to Congress on Thursday, promising that security will be "more important even than the company’s work on artificial intelligence."
Satya Nadella, Microsoft's CEO, "has taken on the responsibility personally to serve as the senior executive with overall accountability for Microsoft’s security," Smith told Congress.
His testimony comes after Microsoft admitted that it could have taken steps to prevent two aggressive nation-state cyberattacks from China and Russia.
The City of Cleveland says emergency services, utilities, and airport are unaffected by a recent cyberattack.
The post City of Cleveland Scrambling to Restore Systems Following Cyberattack appeared first on SecurityWeek.

 Source: www.tdsb.on.ca[/caption]
In its letter of notification sent to parents and guardians, the Toronto District School Board stated that it had launched an investigation with the aid of third-party experts to fully assess the nature and scope of the incident. This includes potential compromise of its networks or breach of sensitive personal information.
[caption id="attachment_77137" align="alignnone" width="1770"]
Source: www.tdsb.on.ca[/caption]
In its letter of notification sent to parents and guardians, the Toronto District School Board stated that it had launched an investigation with the aid of third-party experts to fully assess the nature and scope of the incident. This includes potential compromise of its networks or breach of sensitive personal information.
[caption id="attachment_77137" align="alignnone" width="1770"] Source: www.tdsb.on.ca[/caption]
The letter added, "If it is determined that any personal information has been impacted, we will provide notice to all affected individuals. We understand that news of a cyber incident is concerning, but please know that we are doing everything possible to learn more about what occurred and address this situation.
Source: www.tdsb.on.ca[/caption]
The letter added, "If it is determined that any personal information has been impacted, we will provide notice to all affected individuals. We understand that news of a cyber incident is concerning, but please know that we are doing everything possible to learn more about what occurred and address this situation.


“Urgent requests are severely restricted at around 400 a day. Historically primary care and community services have generated around 10,000 samples a day for testing, which gives you an idea of the scale of the impact.” - SynnovisServices including blood transfusions reportedly remain severely disrupted at Guy's and St Thomas' Hospital and King's College Hospital. Both hospitals are experiencing disruption of pathology services, particularly blood tests.
 Source: Synnovis[/caption]
The pathology service provider is also working with NHS Trust to install laptops at the hub laboratory, which will give them access to the Trust IT systems to return test results electronically.
Source: Synnovis[/caption]
The pathology service provider is also working with NHS Trust to install laptops at the hub laboratory, which will give them access to the Trust IT systems to return test results electronically.

 In its post on darkweb, CyberDragon said, “We are joining the “South Korean Company”. This is a country that has long been promoting Russophobia by supporting the Kyiv regime.” The list of websites reportedly targetted by CyberDragon include:
Shinhan Financial Group: It was founded in September 2001 and is one of South Korea's big five financial groups. Its subsidiaries provide a full range of financial services, including banking, securities, life insurance, and investment banking.
State Korean Import-Export Bank KEXIM: The Export-Import Bank of Korea, also commonly known as the Korea Eximbank (KEXIM), is the official export credit agency of South Korea. The bank was first established in 1976. Its primary purpose is to support South Korea's export-led economy by providing loans, financing mega projects and thereby facilitating economic cooperation with other countries.
[caption id="attachment_77014" align="alignnone" width="1600"]
In its post on darkweb, CyberDragon said, “We are joining the “South Korean Company”. This is a country that has long been promoting Russophobia by supporting the Kyiv regime.” The list of websites reportedly targetted by CyberDragon include:
Shinhan Financial Group: It was founded in September 2001 and is one of South Korea's big five financial groups. Its subsidiaries provide a full range of financial services, including banking, securities, life insurance, and investment banking.
State Korean Import-Export Bank KEXIM: The Export-Import Bank of Korea, also commonly known as the Korea Eximbank (KEXIM), is the official export credit agency of South Korea. The bank was first established in 1976. Its primary purpose is to support South Korea's export-led economy by providing loans, financing mega projects and thereby facilitating economic cooperation with other countries.
[caption id="attachment_77014" align="alignnone" width="1600"] Home Page of Korea Eximbank[/caption]
Korea Customs Service: The Korea Customs Service was established in 1970 and is one of tax organizations in South Korea and is run under the Ministry of Economy and Finance. The headquarters is in Seo District, Daejeon.
Korean National Police: The Korean National Police Agency (KNPA), also known as the Korean National Police (KNP), is one of the national police organizations in South Korea. It is run under the Ministry of the Interior and Safety and is headquartered in Seodaemun, Seoul.
National Tax Service: It is the tax organization in South Korea and is run under the Ministry of Economy and Finance. Its headquarters is in Sejong City.
Like many of the previous attacks carried out by the Cyberdragon hacking group, it is unclear if sensitive data of the organisations listed above was compromised. Prima Facie, it looks like the group carried out a DDoS attack meant to disrupt the platform’s services. None of the organizations have publicly responded to the alleged breach. Most of the organizations too seem to have restored the functioning of its websites, hours after the group claimed to have carried out a cyberattack.
Home Page of Korea Eximbank[/caption]
Korea Customs Service: The Korea Customs Service was established in 1970 and is one of tax organizations in South Korea and is run under the Ministry of Economy and Finance. The headquarters is in Seo District, Daejeon.
Korean National Police: The Korean National Police Agency (KNPA), also known as the Korean National Police (KNP), is one of the national police organizations in South Korea. It is run under the Ministry of the Interior and Safety and is headquartered in Seodaemun, Seoul.
National Tax Service: It is the tax organization in South Korea and is run under the Ministry of Economy and Finance. Its headquarters is in Sejong City.
Like many of the previous attacks carried out by the Cyberdragon hacking group, it is unclear if sensitive data of the organisations listed above was compromised. Prima Facie, it looks like the group carried out a DDoS attack meant to disrupt the platform’s services. None of the organizations have publicly responded to the alleged breach. Most of the organizations too seem to have restored the functioning of its websites, hours after the group claimed to have carried out a cyberattack.


 Source: Dark Web[/caption]
The claim of responsibility was boldly asserted by the IT Army of Ukraine through their Telegram channel. Their message, accompanied by a tone of defiance, boasted of rattling the nerves of their adversaries, even if the anticipated "big bang" did not materialize. Meanwhile, amidst the chaos, there emerged reports of Samara students joining the ranks of cyber vigilantes, highlighting the growing complexity of cybersecurity challenges faced by nations worldwide.
The impact of this SPIEF 2024 cyberattack beyond the St. Petersburg International Economic Forum itself, affecting Solar SC and its crucial role in fortifying the forum's digital infrastructure. The ramifications reverberated not only across the Russian Federation but also rippled through Europe and the UK, highlighting the interconnected nature of contemporary cyber warfare.
Source: Dark Web[/caption]
The claim of responsibility was boldly asserted by the IT Army of Ukraine through their Telegram channel. Their message, accompanied by a tone of defiance, boasted of rattling the nerves of their adversaries, even if the anticipated "big bang" did not materialize. Meanwhile, amidst the chaos, there emerged reports of Samara students joining the ranks of cyber vigilantes, highlighting the growing complexity of cybersecurity challenges faced by nations worldwide.
The impact of this SPIEF 2024 cyberattack beyond the St. Petersburg International Economic Forum itself, affecting Solar SC and its crucial role in fortifying the forum's digital infrastructure. The ramifications reverberated not only across the Russian Federation but also rippled through Europe and the UK, highlighting the interconnected nature of contemporary cyber warfare.


 Source: moretonbay.qld.gov.au[/caption]
Source: moretonbay.qld.gov.au[/caption]
We are experiencing system difficulties with our customer request portal. Our third-party provider is investigating a possible information breach. The cause is yet to be determined but there is no indication this is a cyber attack. We will never contact you via unsolicited calls to request sensitive information. No action is required from you at this stage. We will continue to keep you informed.The notice appears to indicate that the breach stemmed from a third-party provider. The Cyber Express team has reached out to the Moreton Bay Council's Privacy Officer for further information on the breach, however no response has been received as of publication time. The potential scale of the data breach, as well as its impact on residents, is currently unknown. It is also unclear on how many individuals may have accessed the available data before the website had been temporarily taken down and subsequently limited. Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.

 Source: X[/caption]
The claimed Snapchat cyberattack has allegedly resulted in service disruptions in certain countries and the temporary incapacitation of key features within the Snapchat application.
Despite SN Blackmeta's claims, Snapchat has not yet released an official statement about the incident, leaving the details of the cyberattack unconfirmed. The Cyber Express has reached out to the company, and we are currently awaiting their response.
[caption id="attachment_76798" align="alignnone" width="372"]
Source: X[/caption]
The claimed Snapchat cyberattack has allegedly resulted in service disruptions in certain countries and the temporary incapacitation of key features within the Snapchat application.
Despite SN Blackmeta's claims, Snapchat has not yet released an official statement about the incident, leaving the details of the cyberattack unconfirmed. The Cyber Express has reached out to the company, and we are currently awaiting their response.
[caption id="attachment_76798" align="alignnone" width="372"] Source: X[/caption]
Interestingly, this isn't the first time SN Blackmeta has made headlines for their cyber activities.
In the past few days alone, the group has launched attacks on various targets, including the Social Security Administration (SSA) website and Microsoft's OneDrive. These attacks aim to disrupt services and hinder user access, demonstrating the group's proficiency in executing cyber warfare.
The recent surge in cyberattacks by SN Blackmeta comes amidst a backdrop of escalating tensions in the digital world. Other hacktivist groups have also been active, targeting prominent organizations and government entities with coordinated attacks.
Source: X[/caption]
Interestingly, this isn't the first time SN Blackmeta has made headlines for their cyber activities.
In the past few days alone, the group has launched attacks on various targets, including the Social Security Administration (SSA) website and Microsoft's OneDrive. These attacks aim to disrupt services and hinder user access, demonstrating the group's proficiency in executing cyber warfare.
The recent surge in cyberattacks by SN Blackmeta comes amidst a backdrop of escalating tensions in the digital world. Other hacktivist groups have also been active, targeting prominent organizations and government entities with coordinated attacks.



 Source: asec.ahnlab.com[/caption]
When decoded, the VBS script is obfuscated, making it difficult for researchers to analyze. The script saves a PowerShell script into the %Temp% directory and executes it. The running script then downloads the Haartoppens.Eft file, which executes an additional PowerShell script. This script is also obfuscated and is designed to load a shellcode to the wab.exe process.
[caption id="attachment_76666" align="alignnone" width="638"]
Source: asec.ahnlab.com[/caption]
When decoded, the VBS script is obfuscated, making it difficult for researchers to analyze. The script saves a PowerShell script into the %Temp% directory and executes it. The running script then downloads the Haartoppens.Eft file, which executes an additional PowerShell script. This script is also obfuscated and is designed to load a shellcode to the wab.exe process.
[caption id="attachment_76666" align="alignnone" width="638"] Source: asec.ahnlab.com[/caption]
The shellcode maintains its persistence by adding a registry key to the infected system, and then accesses a remote C&C server to load additional instructions. The instructions ultimately download the Remcos RAT malware for execution on infected systems.
Source: asec.ahnlab.com[/caption]
The shellcode maintains its persistence by adding a registry key to the infected system, and then accesses a remote C&C server to load additional instructions. The instructions ultimately download the Remcos RAT malware for execution on infected systems.
 Source: asec.ahnlab.com[/caption]
Remcos is a commercial remote access tool (RAT) that is advertised as a legitimate tool, but has been observed in numerous threat actor campaigns. Successful loading of Remcos opens a backdoor on targeted systems, allowing for complete control.
The researchers have shared the following indicators to help detect and stop this campaign:
IOCs (Indicators of Compromise)
Source: asec.ahnlab.com[/caption]
Remcos is a commercial remote access tool (RAT) that is advertised as a legitimate tool, but has been observed in numerous threat actor campaigns. Successful loading of Remcos opens a backdoor on targeted systems, allowing for complete control.
The researchers have shared the following indicators to help detect and stop this campaign:
IOCs (Indicators of Compromise)

 Special Health Resources website notice[/caption]
If Special Health’s troubles are linked to a cyberattack, they seem to have fared better than the damage sustained by NHS London recently, as cyber attackers seemingly have abandoned long-standing pledges to avoid attacking healthcare systems.
Special Health Resources website notice[/caption]
If Special Health’s troubles are linked to a cyberattack, they seem to have fared better than the damage sustained by NHS London recently, as cyber attackers seemingly have abandoned long-standing pledges to avoid attacking healthcare systems. 

 Source: Dark Web[/caption]
The aftermath of the Central Securities Corporation cyberattack is evident as the company's website remains inaccessible, leaving concerned parties in the dark about the extent of the damage and the company's response. Efforts to reach out to Central Securities Corporation have been impeded by the website's downtime, exacerbating the sense of urgency surrounding the situation.
The cybercriminals behind the Central Securities Corporation cyberattack have brazenly demanded nearly $3 million in ransom, further compounding the company's woes.
This incident highlights the ransomware strain like the Underground Team leverages novel approaches to extort money and exploit sensitive data.
Source: Dark Web[/caption]
The aftermath of the Central Securities Corporation cyberattack is evident as the company's website remains inaccessible, leaving concerned parties in the dark about the extent of the damage and the company's response. Efforts to reach out to Central Securities Corporation have been impeded by the website's downtime, exacerbating the sense of urgency surrounding the situation.
The cybercriminals behind the Central Securities Corporation cyberattack have brazenly demanded nearly $3 million in ransom, further compounding the company's woes.
This incident highlights the ransomware strain like the Underground Team leverages novel approaches to extort money and exploit sensitive data.

 Source: Ascension Via Christi Website[/caption]
The update for Ascension Via Christi St. Francis followed a national update from Ascension, which reported continued progress in restoring systems across its network. The company aims to have systems fully restored across its ministry by Friday, June 14.
Source: Ascension Via Christi Website[/caption]
The update for Ascension Via Christi St. Francis followed a national update from Ascension, which reported continued progress in restoring systems across its network. The company aims to have systems fully restored across its ministry by Friday, June 14.

 Source: Dark Web[/caption]
“This company has taken very poor care of the data entrusted to them by its customers. In the course of a successful attack, we stole a huge amount of data. We also attacked the clients of this company ROCKFORD SCHOOL. Which we have access to thanks to CONTROL NET”, reads the threat actor post.
The leaked information highlights the urgent need for enhanced cybersecurity measures, particularly in industries like construction and education, where sensitive data is at stake.
Source: Dark Web[/caption]
“This company has taken very poor care of the data entrusted to them by its customers. In the course of a successful attack, we stole a huge amount of data. We also attacked the clients of this company ROCKFORD SCHOOL. Which we have access to thanks to CONTROL NET”, reads the threat actor post.
The leaked information highlights the urgent need for enhanced cybersecurity measures, particularly in industries like construction and education, where sensitive data is at stake.

“Cyber-attacks against the U.S. healthcare systems rose 130% in 2023, forcing hospitals to cancel procedures and impacting Americans’ access to critical care. Rural hospitals are particularly hard hit as they are often the sole source of care for the communities they serve and lack trained cyber staff and modern cyber defenses. President Biden is committed to every American having access to the care they need, and effective cybersecurity is a part of that. So, we’re excited to work with Microsoft to launch cybersecurity programs that will provide training, advice and technology to help America’s rural hospitals be safe online.”Alongside Microsoft's efforts, Google also announced that it will provide free cybersecurity advice to rural hospitals and non-profit organizations while also launching a pilot program to match its cybersecurity services with the specific needs of rural healthcare facilities.

 Source: www.blood.co.uk[/caption]
Source: www.blood.co.uk[/caption]
“NHS staff are working around the clock to minimise the significant disruption to patient care following the ransomware cyber-attack and we are sorry to all those who have been impacted. Pathology services are integral to a wide range of treatments and we know that a number of operations and appointments have been cancelled due to this attack. We are still working with hospitals and local GP services to fully assess the disruption, and ensure the data is accurate. In the meantime our advice to patients remains, if you have not been contacted please do continue to attend your appointments.”A senior NHS manager disclosed to the Health Service Journal (HSJ) that the incident was “everyone’s worst nightmare.” As blood has a limited shelf life of 35 days, it is critical that these hospital stocks are continually replenished. More units of O-negative and O-positive blood will be required over the coming weeks to accommodate an anticipated increase in surgeries and procedures due to earlier delays. Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.

 Source: Dark Web[/caption]
The affected organization, as claimed by the threat actor, is the Ministry of Defence of Italy, Ministero Difesa, highlighting the gravity of the situation. The website in question, difesa.it, falls under the purview of this governmental body, making it a matter of national security concern.
With Italy being the impacted country, the ramifications extend to the wider European and UK regions, emphasizing the potential for geopolitical implications.
The post by the threat actor, shared on the cybercrime forum, offers insights into the nature of the RCE vulnerability. However, it lacks substantial evidence to validate the claims made.
The absence of proof raises doubts about the credibility of the assertions and necessitates a thorough investigation into the matter.
Source: Dark Web[/caption]
The affected organization, as claimed by the threat actor, is the Ministry of Defence of Italy, Ministero Difesa, highlighting the gravity of the situation. The website in question, difesa.it, falls under the purview of this governmental body, making it a matter of national security concern.
With Italy being the impacted country, the ramifications extend to the wider European and UK regions, emphasizing the potential for geopolitical implications.
The post by the threat actor, shared on the cybercrime forum, offers insights into the nature of the RCE vulnerability. However, it lacks substantial evidence to validate the claims made.
The absence of proof raises doubts about the credibility of the assertions and necessitates a thorough investigation into the matter.


![]()
 Source: Kadokawa's account[/caption]
Source: Kadokawa's account[/caption]

/hs directory, thereby gaining unrestricted access to the host file system.
The attackers also bind the Docker socket to the container, allowing them to manipulate Docker as if they were on the host machine itself. If the "cmd.cat/chattr" image isn't found, the attackers pull it from the cmd.cat repository.
Once the image is in place, they create a Docker container, executing a base64-encoded script that downloads and executes a malicious binary from their command-and-control (C&C) server. The researchers identified the downloaded binary file as ZiggyStarTux, an open-source IRC botnet based on the Kaiten malware.


 Source: news.uark.edu[/caption]
Researchers from these groups dismantled conventional commercial solar inverters, stripping away existing controls and technology. They then integrated work from different partners while implementing custom-designed controls designed with multiple additional layers of cybersecurity protocols.
The University of Arkansas group then took to solar farms in order to subject these modified inverters to real-world conditions to test them and demonstrate the practicality of their cybersecurity measures.
The collaborative partners for this project include the University of Georgia, Texas A&M Kingsville, University of Illinois Chicago, Argonne National Laboratory, National Renewable Energy Laboratory, General Electric Research, Ozarks Electric, and Today's Power Inc. The collaborative efforts from these groups is a further step to fortifying not only the cybersecurity resilience of solar inverters but also to secure the broader landscape of renewable energy technologies.
Source: news.uark.edu[/caption]
Researchers from these groups dismantled conventional commercial solar inverters, stripping away existing controls and technology. They then integrated work from different partners while implementing custom-designed controls designed with multiple additional layers of cybersecurity protocols.
The University of Arkansas group then took to solar farms in order to subject these modified inverters to real-world conditions to test them and demonstrate the practicality of their cybersecurity measures.
The collaborative partners for this project include the University of Georgia, Texas A&M Kingsville, University of Illinois Chicago, Argonne National Laboratory, National Renewable Energy Laboratory, General Electric Research, Ozarks Electric, and Today's Power Inc. The collaborative efforts from these groups is a further step to fortifying not only the cybersecurity resilience of solar inverters but also to secure the broader landscape of renewable energy technologies.

 Source: X[/caption]
Source: X[/caption]



 Source: asec.ahnlab.com[/caption]
Once the victim clicks on the HTML attachment, a fake message displays in the browser while disguising itself as a Microsoft Word document. This message directs the user to click on a "How to fix" button that purports to help them load the document offline. After clicking the button, a set of instructions prompt the user to type out a set of keyboard commands—first type [Win+R], then [Ctrl+V], and press [Enter].
[caption id="attachment_75494" align="alignnone" width="1200"]
Source: asec.ahnlab.com[/caption]
Once the victim clicks on the HTML attachment, a fake message displays in the browser while disguising itself as a Microsoft Word document. This message directs the user to click on a "How to fix" button that purports to help them load the document offline. After clicking the button, a set of instructions prompt the user to type out a set of keyboard commands—first type [Win+R], then [Ctrl+V], and press [Enter].
[caption id="attachment_75494" align="alignnone" width="1200"] Source: asec.ahnlab.com[/caption]
The button may alternatively load a different set of instructions directing the user to manually access the Windows PowerShell terminal and hit right-click within the terminal window. By following the instructions, the victim inadvertently pastes a malicious script to the terminal, which then executes in their system.
Source: asec.ahnlab.com[/caption]
The button may alternatively load a different set of instructions directing the user to manually access the Windows PowerShell terminal and hit right-click within the terminal window. By following the instructions, the victim inadvertently pastes a malicious script to the terminal, which then executes in their system.
 Source: asec.ahnlab.com[/caption]
Source: asec.ahnlab.com[/caption]

 E-T-A Elektrotechnische Apparate GmbH operates six production facilities and has a presence in 60 countries worldwide. The company’s product range includes a variety of electrical protection solutions essential to numerous industries. The company is renowned for manufacturing circuit breakers, electronic circuit protectors, and various other electronic components.
Despite the ransomware group's claims, the company's official website appeared to be fully functional, and there were no signs of foul play. Further to verify Akira's cyberattack on E-T-A claims, The Cyber Express Team reached out to E-T-A Elektrotechnische Apparate GmbH for an official statement.
As of the time of writing, no response has been received from the company. This leaves the ransomware claims unverified, with no confirmation or denial from E-T-A's officials.
E-T-A Elektrotechnische Apparate GmbH operates six production facilities and has a presence in 60 countries worldwide. The company’s product range includes a variety of electrical protection solutions essential to numerous industries. The company is renowned for manufacturing circuit breakers, electronic circuit protectors, and various other electronic components.
Despite the ransomware group's claims, the company's official website appeared to be fully functional, and there were no signs of foul play. Further to verify Akira's cyberattack on E-T-A claims, The Cyber Express Team reached out to E-T-A Elektrotechnische Apparate GmbH for an official statement.
As of the time of writing, no response has been received from the company. This leaves the ransomware claims unverified, with no confirmation or denial from E-T-A's officials.

 Source: Facebook[/caption]
The Facebook user pointed out several gaps in ARRL cyberattack updates, such as the absence of information about the phone systems being down and the lack of a communication path for interim assistance.
Source: Facebook[/caption]
The Facebook user pointed out several gaps in ARRL cyberattack updates, such as the absence of information about the phone systems being down and the lack of a communication path for interim assistance.

 Source: Telangana Police Website[/caption]
The TSCOP App Cyberattack was masterminded by a threat actor who goes by the name “Adm1nFr1end.” The same thread actor was responsible for Telangana Police’s Hawk Eye app data breach last week.
The claims of cyberattack on the TSCOP app emerged on June 5, 2024, when the TA posted the alleged leaked data on BreachForums site.
According to the TA, the leaked data includes the names, phone numbers and email addresses of police personnel from the Anti-Corruption Bureau, the Anti-Narcotics Bureau, Intelligence, Greyhounds (counter-insurgency wing against terrorists), Home Guards, and a host of other wings of the Telangana Police.
Source: Telangana Police Website[/caption]
The TSCOP App Cyberattack was masterminded by a threat actor who goes by the name “Adm1nFr1end.” The same thread actor was responsible for Telangana Police’s Hawk Eye app data breach last week.
The claims of cyberattack on the TSCOP app emerged on June 5, 2024, when the TA posted the alleged leaked data on BreachForums site.
According to the TA, the leaked data includes the names, phone numbers and email addresses of police personnel from the Anti-Corruption Bureau, the Anti-Narcotics Bureau, Intelligence, Greyhounds (counter-insurgency wing against terrorists), Home Guards, and a host of other wings of the Telangana Police.

 But what could be major concern to the police is the leak of data related to criminals who were recently booked. The TA shared samples of offenders who were recently booked, which revealed the operations carried out by the concerned police station, the names, ages, mobile numbers, and addresses of the accused, the date on which they were booked, and in a few cases, the crime for which they were booked.
The hacker also shared another sample, which could be of critical concern owing to breach of privacy of citizens. This data breach revealed the names, addresses, voter ids, date of birth and license number of citizens who had applied for a gun license and the reason for holding a weapon.
But what could be major concern to the police is the leak of data related to criminals who were recently booked. The TA shared samples of offenders who were recently booked, which revealed the operations carried out by the concerned police station, the names, ages, mobile numbers, and addresses of the accused, the date on which they were booked, and in a few cases, the crime for which they were booked.
The hacker also shared another sample, which could be of critical concern owing to breach of privacy of citizens. This data breach revealed the names, addresses, voter ids, date of birth and license number of citizens who had applied for a gun license and the reason for holding a weapon.

 Source: X[/caption]
The Cyber Express has reached out to the Telangana Police, seeking their response on the cyberattack. We will update this story as we get more information.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.
Source: X[/caption]
The Cyber Express has reached out to the Telangana Police, seeking their response on the cyberattack. We will update this story as we get more information.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.

"The immediate impact was reported on patients using NHS services within the two partner hospitals, as well as GP services across Bexley, Greenwich, Lewisham, Bromley, Southwark and Lambeth boroughs."
"We are currently experiencing disruption to our pathology services, particularly blood tests.""This is following a cyber attack affecting our pathology service provider Synnovis," said the NHS statement. "Very regrettably we have had to cancel some procedures and operations. We apologise unreservedly to all patients who are affected." The disruption in the blood transfusion IT system poses a risk to trauma cases, with only urgent blood components being transfused when critically necessary for patients. Efforts are underway by the Department of Health and Social Care, NHS England, and the National Cyber Security Centre to address the cyber incident and support affected organizations while prioritizing patient safety. The uncertainty surrounding the duration of the disruption raises concerns about resource availability and potential further critical incidents. The attack follows a similar one that hit NHS services in Scotland in March.
"It is still early days and we are trying to understand exactly what has happened."A taskforce of IT experts from Synnovis and the NHS is working to fully assess the impact this has had, and to take the appropriate action needed. We are working closely with NHS Trust partners to minimise the impact on patients and other service users."
"Regrettably this is affecting patients, with some activity already cancelled or redirected to other providers as urgent work is prioritised.""We are incredibly sorry for the inconvenience and upset this is causing to patients, service users and anyone else affected. We are doing our best to minimise the impact and will stay in touch with local NHS services to keep people up to date with developments," Dollar added. Synnovis has invested heavily in ensuring that IT arrangements are of the highest order of safety but Dollar, citing the ransomware attack, said, "This is a harsh reminder that this sort of attack can happen to anyone at any time and that, dispiritingly, the individuals behind it have no scruples about who their actions might affect." As the healthcare sector continues to navigate the evolving landscape of cyber threats, stakeholders must remain vigilant, prioritize cybersecurity protocols, and collaborate to fortify defenses against ransomware attacks. Safeguarding patient data and preserving the trust of individuals relying on healthcare services are critical imperatives in the ongoing battle against cybercrime in the healthcare industry.

 Source: Dark Web[/caption]
The cyberattack on Northern Minerals has raised questions not only for the organization but also for stakeholders and investors, as many businesses and individuals have invested heavily in these mining projects.
Prior to the current situation, Northern Minerals discovered a data breach incident in late March that compromised a range of sensitive data, including corporate, operational, and financial information, as well as details about current and former personnel and shareholders.
Despite the severity of the breach, Northern Minerals reported that its operations and broader systems remained largely unaffected. However, the BianLian group has leaked data it says was compromised in the attack, including operational, strategic, R&D, financial, and employee information, along with executive emails and phone numbers.
Treasurer Jim Chalmers' directive to Chinese-linked investors, including Yuxiao Fund, to sell their stakes in Northern Minerals is a significant move to safeguard Australia's national interests. The Foreign Investment Review Board advised this action to ensure compliance with Australia's foreign investment framework. The decision affects not only Yuxiao Fund but also other foreign shareholders, who have been given 60 days to dispose of their shares.
Yuxiao Fund, a Singapore-registered private investment vehicle of Chinese national Wu Yuxiao, had previously been restricted from increasing its stake in Northern Minerals. The Australian government's insistence on these divestitures reflects a broader strategy to reduce dependency on foreign entities, particularly those linked to China, in the critical minerals sector.
Source: Dark Web[/caption]
The cyberattack on Northern Minerals has raised questions not only for the organization but also for stakeholders and investors, as many businesses and individuals have invested heavily in these mining projects.
Prior to the current situation, Northern Minerals discovered a data breach incident in late March that compromised a range of sensitive data, including corporate, operational, and financial information, as well as details about current and former personnel and shareholders.
Despite the severity of the breach, Northern Minerals reported that its operations and broader systems remained largely unaffected. However, the BianLian group has leaked data it says was compromised in the attack, including operational, strategic, R&D, financial, and employee information, along with executive emails and phone numbers.
Treasurer Jim Chalmers' directive to Chinese-linked investors, including Yuxiao Fund, to sell their stakes in Northern Minerals is a significant move to safeguard Australia's national interests. The Foreign Investment Review Board advised this action to ensure compliance with Australia's foreign investment framework. The decision affects not only Yuxiao Fund but also other foreign shareholders, who have been given 60 days to dispose of their shares.
Yuxiao Fund, a Singapore-registered private investment vehicle of Chinese national Wu Yuxiao, had previously been restricted from increasing its stake in Northern Minerals. The Australian government's insistence on these divestitures reflects a broader strategy to reduce dependency on foreign entities, particularly those linked to China, in the critical minerals sector.

"At this time, we have no indication that the general public's information was accessed."

“The threat from China [to Canadian organizations] is very likely the most significant by volume, capability, and assessed intent. China-sponsored cyber threat actors will very likely continue targeting industries and technologies in Canada that contribute to the state’s strategic priorities.”
 Source: Canadian National Threat Assessment Report 2023-24[/caption]
Source: Canadian National Threat Assessment Report 2023-24[/caption]
“Canada’s strong democratic institutions, advanced economy, innovative research sectors, and leading academic institutions make Canada an attractive target for cyber-enabled espionage, sabotage, and foreign influenced activities, all of which pose significant threats to Canada’s national security,” the report said.The report identified China as a state-based threat conducting widespread cyberespionage across various sectors, including government, academia, private industry, and civil society organizations. The Cyber Centre also shares concerns with the U.S. about PRC cyber threat groups pre-positioning network access for potential attacks on North American critical infrastructure in case of conflict in the Indo-Pacific.
"The Cyber Centre assesses that the direct threat to Canada’s critical infrastructure from PRC state-sponsored actors is likely lower than that to U.S. infrastructure, but should U.S. infrastructure be disrupted, Canada would likely be affected as well due to interoperability and interdependence in the sectors of greatest concern."Sectors of greatest concern include energy, telecommunications, and transportation. However, the prelude to the attacks on the provincial government networks also saw the targeting of the healthcare sector in the country, which makes it a cause of concern too. The first of the attacks in this sector was on the retail and pharmacy chain London Drugs, followed by a cyberattack on the First Nations Health Authority (FNHA), which compromised its employee information and limited personal data.

Three-quarters of SMBs fear that a cyberattack could put them out of business. For good reason: 96% of them have already been the victims of a cyberattack.
The post Cyberattack Risks Keep Small Business Security Teams on Edge appeared first on Security Boulevard.

 Virus Total Scan of Suspected IP [159.65.76.209] (Source: samcurry.net)[/caption]This led him to believe the incident was much more complicated than a mere localized attack scenario. When the researcher attempted to isolate the intrusion by switching between cloud providers such as AWS (Amazon Web Services) and GCP (Google Cloud Platform), the suspicious activity remained. This led him to suspect that his modem had been compromised.
Sam traced the suspicious IP address to Digital Ocean and shared his findings three years later on vacation with his friends, who worked for various threat intelligence companies - and together they proceeded to find out how big the problem was. The researchers were able to link this suspicious IP address to a history of malicious usage such as involvement in hosting content for targeted phishing campaigns on ISG Latam (a South American cybersecurity company), as well as Adidas.
The IP address had been used to host over 1,000 domains, all of which followed a pattern of a name followed by six numbers and the top-level domain. This pattern suggests the usage of a domain generation algorithm by the malware operators to rotate C&C server addresses for additional obfuscation.
[caption id="attachment_74327" align="alignnone" width="1478"]
Virus Total Scan of Suspected IP [159.65.76.209] (Source: samcurry.net)[/caption]This led him to believe the incident was much more complicated than a mere localized attack scenario. When the researcher attempted to isolate the intrusion by switching between cloud providers such as AWS (Amazon Web Services) and GCP (Google Cloud Platform), the suspicious activity remained. This led him to suspect that his modem had been compromised.
Sam traced the suspicious IP address to Digital Ocean and shared his findings three years later on vacation with his friends, who worked for various threat intelligence companies - and together they proceeded to find out how big the problem was. The researchers were able to link this suspicious IP address to a history of malicious usage such as involvement in hosting content for targeted phishing campaigns on ISG Latam (a South American cybersecurity company), as well as Adidas.
The IP address had been used to host over 1,000 domains, all of which followed a pattern of a name followed by six numbers and the top-level domain. This pattern suggests the usage of a domain generation algorithm by the malware operators to rotate C&C server addresses for additional obfuscation.
[caption id="attachment_74327" align="alignnone" width="1478"] Source: samcurry.net[/caption]
The researcher said it was challenging to understand the attacker's intent, as they had targeted ISG Latam, Adidas and his own modem through the use of the same IP address.
Source: samcurry.net[/caption]
The researcher said it was challenging to understand the attacker's intent, as they had targeted ISG Latam, Adidas and his own modem through the use of the same IP address.
 Exposed Hidden API Calls of COX Modems (Source: samcurry.net)[/caption]
The researcher was able to exploit the router configuration page to load hidden API documentation, exposing an underlying vulnerability that could theoretically grant hackers control over the modems of millions of Cox customers.
Curry disclosed these findings to Cox through their responsible disclosure page. The disclosure led Cox to take down the vulnerable API calls within six hours, with the researcher confirming that they were no longer able to reproduce any of the discovered vulnerabilities the day after.
Cox stated that the reported API vector was not observed being exploited in the past, but confirmed that they had no affiliation with the reported DigitalOcean IP address. The researcher stated that this indicated that his device had been compromised through an alternative method than disclosed in his blog and to the ISP service.
The compromise of the researcher's device along with his own disclosure after discovering vulnerabilities in the modem's hidden API calls are examples of the inherent risks in remotely managed systems.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.
Exposed Hidden API Calls of COX Modems (Source: samcurry.net)[/caption]
The researcher was able to exploit the router configuration page to load hidden API documentation, exposing an underlying vulnerability that could theoretically grant hackers control over the modems of millions of Cox customers.
Curry disclosed these findings to Cox through their responsible disclosure page. The disclosure led Cox to take down the vulnerable API calls within six hours, with the researcher confirming that they were no longer able to reproduce any of the discovered vulnerabilities the day after.
Cox stated that the reported API vector was not observed being exploited in the past, but confirmed that they had no affiliation with the reported DigitalOcean IP address. The researcher stated that this indicated that his device had been compromised through an alternative method than disclosed in his blog and to the ISP service.
The compromise of the researcher's device along with his own disclosure after discovering vulnerabilities in the modem's hidden API calls are examples of the inherent risks in remotely managed systems.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information. 
