Copilot+ Recall is ‘Dumbest Cybersecurity Move in a Decade’: Researcher


Read more of this story at Slashdot.
SecurityWeek editor-at-large Ryan Naraine examines the broad tension between tech innovation and privacy rights at a time when ChatGPT-like bots and generative-AI apps are starting to dominate the landscape.
The post Microsoft’s Windows Recall: Cutting-Edge Search Tech or Creepy Overreach? appeared first on SecurityWeek.

 'No Defender' Windows Defender bypass[/caption]
The GitHub project, simply called “No Defender,” is billed as “A fun way to disable windows defender + firewall.”
In a note on the project, repository owner “es3n1n” said they essentially reverse-engineered the API that antivirus vendors use to disable Windows Defender.
“There's a WSC (Windows Security Center) service in Windows which is used by antiviruses to let Windows know that there's some other antivirus in the hood and it should disable Windows Defender,” the note states.
“This WSC API is undocumented and furthermore requires people to sign an NDA with Microsoft to get its documentation, so I decided to take an interesting approach for such a thing and used an already existing antivirus called Avast. This AV engine includes a so-called wsc_proxy.exe service, which essentially sets up the WSC API for Avast. With a little bit of reverse engineering, I turned this service into a service that could add my own stuff there.”
One limitation noted by es3n1n is that “to keep this WSC stuff even after reboot, no-defender adds itself (not really itself but rather Avast's module) to the autorun. Thus, you would need to keep the no-defender binaries on your disk.”
'No Defender' Windows Defender bypass[/caption]
The GitHub project, simply called “No Defender,” is billed as “A fun way to disable windows defender + firewall.”
In a note on the project, repository owner “es3n1n” said they essentially reverse-engineered the API that antivirus vendors use to disable Windows Defender.
“There's a WSC (Windows Security Center) service in Windows which is used by antiviruses to let Windows know that there's some other antivirus in the hood and it should disable Windows Defender,” the note states.
“This WSC API is undocumented and furthermore requires people to sign an NDA with Microsoft to get its documentation, so I decided to take an interesting approach for such a thing and used an already existing antivirus called Avast. This AV engine includes a so-called wsc_proxy.exe service, which essentially sets up the WSC API for Avast. With a little bit of reverse engineering, I turned this service into a service that could add my own stuff there.”
One limitation noted by es3n1n is that “to keep this WSC stuff even after reboot, no-defender adds itself (not really itself but rather Avast's module) to the autorun. Thus, you would need to keep the no-defender binaries on your disk.”

Source: www.proofpoint.com – Author: 1 Microsoft has come under fire recently from both the U.S. government and rival companies for its failure to stop a Chinese hack of its systems last summer. One change the tech giant is making in response: linking executive compensation more closely to cybersecurity. In April, a government review board described […]
La entrada A Microsoft under attack from government and tech rivals after ‘preventable’ hack ties executive pay to cyberthreats – Source: www.proofpoint.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

“Microsoft assesses that Moonstone Sleet’s objective in deploying the ransomware is financial gain, suggesting the actor conducts cyber operations for both intelligence collection and revenue generation.”FakePenny ransomware demands exorbitant ransoms, with recent demands reaching $6.6 million in Bitcoin. “This is in stark contrast to the lower ransom demands of previous North Korea ransomware attacks, like WannaCry 2.0 and H0lyGh0st,” Microsoft said. Notably, the ransom note used by FakePenny ransomware closely resembles the one employed in the infamous NotPetya ransomware attack, which is attributed to the North Korean group Seashell Blizzard. This continuity in tactics highlights the interconnected nature of North Korean cyber operations.
“Despite being new, Moonstone Sleet has demonstrated that it will continue to mature, develop, and evolve, and has positioned itself to be a preeminent threat actor conducting sophisticated attacks on behalf of the North Korean regime.”
Read more of this story at Slashdot.

Source: securityboulevard.com – Author: Wajahat Raja Recent reports claim that the Microsoft Threat Intelligence team stated that a cybercriminal group, identified as Storm-1811, has been exploiting Microsoft’s Quick Assist tool in a series of social engineering attacks. This group is known for deploying the Black Basta ransomware attack. On May 15, 2024, Microsoft released details […]
La entrada Black Basta Ransomware Attack: Microsoft Quick Assist Flaw – Source: securityboulevard.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.
Recent reports claim that the Microsoft Threat Intelligence team stated that a cybercriminal group, identified as Storm-1811, has been exploiting Microsoft’s Quick Assist tool in a series of social engineering attacks. This group is known for deploying the Black Basta ransomware attack. On May 15, 2024, Microsoft released details about how this financially motivated group […]
The post Black Basta Ransomware Attack: Microsoft Quick Assist Flaw appeared first on TuxCare.
The post Black Basta Ransomware Attack: Microsoft Quick Assist Flaw appeared first on Security Boulevard.
Read more of this story at Slashdot.
Episode 331 of the Shared Security Podcast discusses privacy and security concerns related to two major technological developments: the introduction of Windows PC’s new feature ‘Recall,’ part of Microsoft’s Copilot+, which captures desktop screenshots for AI-powered search tools, and Slack’s policy of using user data to train machine learning features with users opted in by […]
The post Microsoft’s Copilot+ Recall Feature, Slack’s AI Training Controversy appeared first on Shared Security Podcast.
The post Microsoft’s Copilot+ Recall Feature, Slack’s AI Training Controversy appeared first on Security Boulevard.
Read more of this story at Slashdot.
These sources, as clearly stated in the repo’s readme, are the 8088 assembly language sources from 10th Feb 1983, and are being open-sourced for historical reference and educational purposes. This means we will not be accepting PRs that modify the source in any way.
↫ Rich Turner
I’m loving all these open source releases from Microsoft, but honestly, I’d wish the pace was a little higher and we’d get to some more recent stuff. Open sourcing early versions of MS-DOS and related software is obviously great from a software preservation standpoint, but at this rate we’ll get to more influential pieces of software by the time the sun experiences its helium flash.
On a related note, about a month ago Microsoft released the source code to MS-DOS 4.00. Well, we’ve now also got access to the code for MS-DOS 4.01, a bugfix release that came out very quickly after 4.00.
Due to various bugs, DOS 4.00 was a relatively short-lived release, and it was replaced by DOS 4.01 just a couple of months later.
Howard M. Harte (hharte), who already fixed various flaws in the official source code release of MS-DOS 4.00, managed to figure out the differences between DOS 4.00 and 4.01 — we now have access to the improved version as well!
↫ Lothar Serra Mari
We’re getting a pretty complete picture of early MS-DOS source code.
Read more of this story at Slashdot.
Source: www.govinfosecurity.com – Author: 1 Standards, Regulations & Compliance March Decision Mandated Commission to Stem Data Flows From Its Office 365 Use Akshaya Asokan (asokan_akshaya) • May 24, 2024 The European Commission is appealing a decision that might make it impossible for it to use Microsoft 365. (Image: Shutterstock) The European Commission is […]
La entrada EU Commission and Microsoft Appeal EDPS Office 365 Decision – Source: www.govinfosecurity.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: securityaffairs.com – Author: Pierluigi Paganini Recall feature in Microsoft Copilot+ PCs raises privacy and security concerns UK data watchdog is investigating Microsoft regarding the new Recall feature in Copilot+ PCs that captures screenshots of the user’s laptop every few seconds. The UK data watchdog, the Information Commissioner’s Office (ICO), is investigating a new feature, […]
La entrada Recall feature in Microsoft Copilot+ PCs raises privacy and security concerns – Source: securityaffairs.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: www.infosecurity-magazine.com – Author: 1 Microsoft has warned retailers and restaurants of sophisticated gift card fraud which can cost victims up to $100,000 a day. In a new Cyber Signals report, the tech giant highlighted a 30% rise in intrusion activity by the threat actor Storm-0539 between March and May 2024. The group, which operates […]
La entrada Microsoft: Gift Card Fraud Rising, Costing Businesses up to $100,000 a Day – Source: www.infosecurity-magazine.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: www.techrepublic.com – Author: Cedric Pernet A new report from IBM X-Force exposes changes in the Grandoreiro malware landscape. The banking trojan is now capable of targeting more than 1,500 global banks in more than 60 countries, and it has been updated with new features. Also, Grandoreiro’s targeting has become wider, as it initially only […]
La entrada IBM X-Force Report: Grandoreiro Malware Targets More Than 1,500 Banks in 60 Countries – Source: www.techrepublic.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: www.schneier.com – Author: Bruce Schneier Microsoft is trying to create a personal digital assistant: At a Build conference event on Monday, Microsoft revealed a new AI-powered feature called “Recall” for Copilot+ PCs that will allow Windows 11 users to search and retrieve their past activities on their PC. To make it work, Recall records […]
La entrada Personal AI Assistants and Privacy – Source: www.schneier.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.
Enlarge (credit: Getty Images)
Bing, Microsoft's search engine platform, went down in the very early morning today. That meant that searches from Microsoft's Edge browsers that had yet to change their default providers didn't work. It also meant that services relying on Bing's search API—Microsoft's own Copilot, ChatGPT search, Yahoo, Ecosia, and DuckDuckGo—similarly failed.
Services were largely restored by the morning Eastern work hours, but the timing feels apt, concerning, or some combination of the two. Google, the consistently dominating search platform, just last week announced and debuted AI Overviews as a default addition to all searches. If you don't want an AI response but still want to use Google, you can hunt down the new "Web" option in a menu, or you can, per Ernie Smith, tack "&udm=14" onto your search or use Smith's own "Konami code" shortcut page.
If dismay about AI's hallucinations, power draw, or pizza recipes concern you—along with perhaps broader Google issues involving privacy, tracking, news, SEO, or monopoly power—most of your other major options were brought down by a single API outage this morning. Moving past that kind of single point of vulnerability will take some work, both by the industry and by you, the person wondering if there's a real alternative.
Microsoft is trying to create a personal digital assistant:
At a Build conference event on Monday, Microsoft revealed a new AI-powered feature called “Recall” for Copilot+ PCs that will allow Windows 11 users to search and retrieve their past activities on their PC. To make it work, Recall records everything users do on their PC, including activities in apps, communications in live meetings, and websites visited for research. Despite encryption and local storage, the new feature raises privacy concerns for certain Windows users.
I wrote about this AI trust problem last year:
One of the promises of generative AI is a personal digital assistant. Acting as your advocate with others, and as a butler with you. This requires an intimacy greater than your search engine, email provider, cloud storage system, or phone. You’re going to want it with you 24/7, constantly training on everything you do. You will want it to know everything about you, so it can most effectively work on your behalf.
And it will help you in many ways. It will notice your moods and know what to suggest. It will anticipate your needs and work to satisfy them. It will be your therapist, life coach, and relationship counselor.
You will default to thinking of it as a friend. You will speak to it in natural language, and it will respond in kind. If it is a robot, it will look humanoid—or at least like an animal. It will interact with the whole of your existence, just like another person would.
[…]
And you will want to trust it. It will use your mannerisms and cultural references. It will have a convincing voice, a confident tone, and an authoritative manner. Its personality will be optimized to exactly what you like and respond to.
It will act trustworthy, but it will not be trustworthy. We won’t know how they are trained. We won’t know their secret instructions. We won’t know their biases, either accidental or deliberate.
We do know that they are built at enormous expense, mostly in secret, by profit-maximizing corporations for their own benefit.
[…]
All of this is a long-winded way of saying that we need trustworthy AI. AI whose behavior, limitations, and training are understood. AI whose biases are understood, and corrected for. AI whose goals are understood. That won’t secretly betray your trust to someone else.
The market will not provide this on its own. Corporations are profit maximizers, at the expense of society. And the incentives of surveillance capitalism are just too much to resist.
We are going to need some sort of public AI to counterbalance all of these corporate AIs.
EDITED TO ADD (5/24): Lots of comments about Microsoft Recall and security:
This:
Because Recall is “default allow” (it relies on a list of things not to record) … it’s going to vacuum up huge volumes and heretofore unknown types of data, most of which are ephemeral today. The “we can’t avoid saving passwords if they’re not masked” warning Microsoft included is only the tip of that iceberg. There’s an ocean of data that the security ecosystem assumes is “out of reach” because it’s either never stored, or it’s encrypted in transit. All of that goes out the window if the endpoint is just going to…turn around and write it to disk. (And local encryption at rest won’t help much here if the data is queryable in the user’s own authentication context!)
This:
The fact that Microsoft’s new Recall thing won’t capture DRM content means the engineers do understand the risk of logging everything. They just chose to preference the interests of corporates and money over people, deliberately.
This:
Microsoft Recall is going to make post-breach impact analysis impossible. Right now IR processes can establish a timeline of data stewardship to identify what information may have been available to an attacker based on the level of access they obtained. It’s not trivial work, but IR folks can do it. Once a system with Recall is compromised, all data that has touched that system is potentially compromised too, and the ML indirection makes it near impossible to confidently identify a blast radius.
This:
You may be in a position where leaders in your company are hot to turn on Microsoft Copilot Recall. Your best counterargument isn’t threat actors stealing company data. It’s that opposing counsel will request the recall data and demand it not be disabled as part of e-discovery proceedings.

Source: www.bleepingcomputer.com – Author: Mayank Parmar A massive Microsoft outage affects Bing.com, Copilot for web and mobile, Copilot in Windows, ChatGPT internet search and DuckDuckGo. Microsoft outage started at approximately 3 AM EDT and seems to have primarily affected users in Asia and Europe. According to user reports and our tests, if you try to open Bing.com, […]
La entrada Microsoft outage affects Bing, Copilot, DuckDuckGo and ChatGPT internet search – Source: www.bleepingcomputer.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Source: thehackernews.com – Author: . May 23, 2024NewsroomEndpoint Security / Data Privacy Microsoft on Wednesday outlined its plans to deprecate Visual Basic Script (VBScript) in the second half of 2024 in favor of more advanced alternatives such as JavaScript and PowerShell. “Technology has advanced over the years, giving rise to more powerful and versatile scripting […]
La entrada The End of an Era: Microsoft Phases Out VBScript for JavaScript and PowerShell – Source:thehackernews.com se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP.

Enlarge (credit: Microsoft)
Here at Ars, we’ve been around long enough to chronicle every single time that Microsoft has tried to get Windows running on Arm-based processors, instead of the Intel and AMD-made x86 chips that have been synonymous with Windows for more than three decades. The most significant attempts happened in 2012 with Windows RT, which looked like Windows 8 but couldn’t run any x86 Windows apps; and in 2017 when Windows 10 Arm PCs arrived with rudimentary x86 emulation.
The main PC company backing each of those Arm efforts was Microsoft itself, which launched the original Surface to showcase Windows RT and the first Surface Pro X during the Windows 10 era. Since then, Microsoft has periodically refreshed the Arm version of the Surface tablet while continuing to sell Intel versions. A couple of PC OEMs put out Windows RT tablets, and most of them took a stab at one or two Windows 10-into-11-era Arm PCs. But there was never a big unified push that made it clear that the entire consumer PC ecosystem had bought into Arm.
This week’s announcements felt different—yes, there was a new Surface Pro and Surface Laptop from Microsoft leading the charge (and the new Surface Pro is the first Surface Pro ever to ship Arm as the default option for most people). But the Surface launch was accompanied by a major wave of systems from essentially every major PC OEM, suggesting at least some level of elevated enthusiasm for the Snapdragon X series that didn’t exist for older Arm chips.
‘I am not a typo’ campaign is calling for technology companies to make autocorrect less ‘western- and white-focused’
People whose names get mangled by autocorrect have urged technology companies to fix the problem faster, with one person whose name gets switched to “Satan” saying: “I am tired of it.”
People with Irish, Indian and Welsh names are among those calling for improvements to the systems that operate on phones and computers as part of the “I am not a typo” campaign.
Continue reading...© Photograph: Yuri Arcurs/Alamy
© Photograph: Yuri Arcurs/Alamy
Developing an AI-powered threat to security, privacy, and identity is certainly a choice, but it’s one that Microsoft was willing to make this week at its “Build” developer conference.
On Monday, the computing giant unveiled a new line of PCs that integrate Artificial Intelligence (AI) technology to promise faster speeds, enhanced productivity, and a powerful data collection and search tool that screenshots a device’s activity—including password entry—every few seconds.
This is “Recall,” a much-advertised feature within what Microsoft is calling its “Copilot+ PCs,” a reference to the AI assistant and companion which the company released in late 2023. With Recall on the new Copilot+ PCs, users no longer need to manage and remember their own browsing and chat activity. Instead, by regularly taking and storing screenshots of a user’s activity, the Copilot+ PCs can comb through that visual data to deliver answers to natural language questions, such as “Find the site with the white sneakers,” and “blue pantsuit with a sequin lace from abuelita.”
As any regularly updated repository of device activity poses an enormous security threat—imagine hackers getting access to a Recall database and looking for, say, Social Security Numbers, bank account info, and addresses—Microsoft has said that all Recall screenshots are encrypted and stored locally on a device.
But, in terms of security, that’s about all users will get, as Recall will not detect and obscure passwords, shy away from recording pornographic material, or turn a blind eye to sensitive information.
“Note that Recall does not perform content moderation. It will not hide information such as passwords or financial account numbers. That data may be in snapshots that are stored on your device, especially when sites do not follow standard internet protocols like cloaking password entry.”
The consequences of such a system could be enormous.
With Recall, a CEO’s personal laptop could become an even more enticing target for hackers equipped with infostealers, a journalist’s protected sources could be within closer grasp of an oppressive government that isn’t afraid to target dissidents with malware, and entire identities could be abused and impersonated by a separate device user.
In fact, Recall seems to only work best in a one-device-per-person world. Though Microsoft explained that its Copilot+ PCs will only record Recall snapshots to specific device accounts, plenty of people share devices and accounts. For the domestic abuse survivor who is forced to share an account with their abuser, for the victim of theft who—like many people—used a weak device passcode that can easily be cracked, and for the teenager who questions their identity on the family computer, Recall could be more of a burden than a benefit.
For Malwarebytes General Manager of Consumer Business Unit Mark Beare, Recall raises yet another issue:
“I worry that we are heading to a social media 2.0 like world.”
When users first raced to upload massive quantities of sensitive, personal data onto social media platforms more than 10 years ago, they couldn’t predict how that data would be scrutinized in the future, or how it would be scoured and weaponized by cybercriminals, Beare said.
“With AI there will be a strong pull to put your full self into a model (so it knows you),” Beare said. “I don’t think it’s easy to understand all the negative aspects of what can happen from doing that and how bad actors can benefit.”
We don’t just report on threats – we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your—and your family’s—personal information by using identity protection.
Read more of this story at Slashdot.
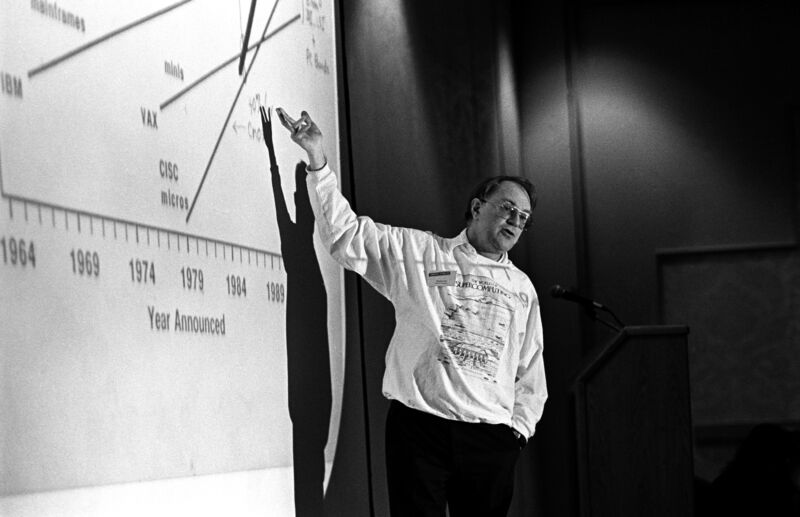
Enlarge / A photo of Gordon Bell speaking at the annual PC Forum in Palm Springs, California, March 1989. (credit: Ann E. Yow-Dyson/Getty Images)
Computer pioneer Gordon Bell, who as an early employee of Digital Equipment Corporation (DEC) played a key role in the development of several influential minicomputer systems and also co-founded the first major computer museum, passed away on Friday, according to Bell Labs veteran John Mashey. Mashey announced Bell's passing in a social media post on Tuesday morning.
"I am very sad to report [the] death May 17 at age 89 of Gordon Bell, famous computer pioneer, a founder of Computer Museum in Boston, and a force behind the @ComputerHistory here in Silicon Valley, and good friend since the 1980s," wrote Mashey in his announcement. "He succumbed to aspiration pneumonia in Coronado, CA."
Bell was a pivotal figure in the history of computing and a notable champion of tech history, having founded Boston's Computer Museum in 1979, which later became the heart of the Computer History Museum in Mountain View, with his wife Gwen Bell. He was also the namesake of the ACM's prestigious Gordon Bell Prize, created to spur innovations in parallel processing.
Read more of this story at Slashdot.
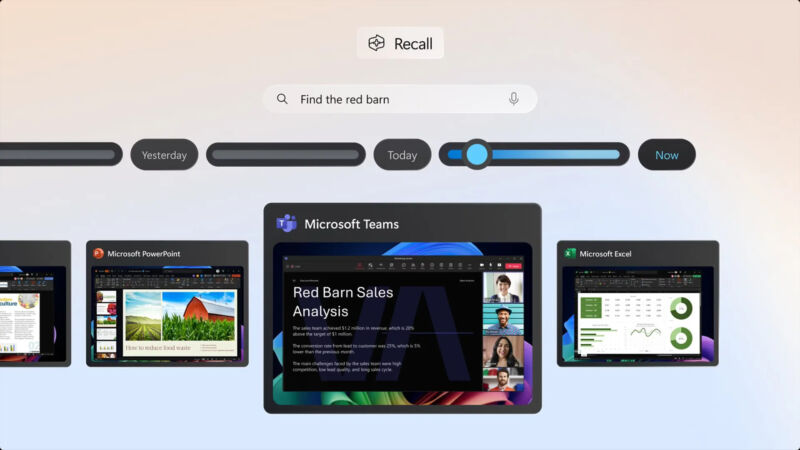
Enlarge / A screenshot of Microsoft's new "Recall" feature in action. (credit: Microsoft)
At a Build conference event on Monday, Microsoft revealed a new AI-powered feature called "Recall" for Copilot+ PCs that will allow Windows 11 users to search and retrieve their past activities on their PC. To make it work, Recall records everything users do on their PC, including activities in apps, communications in live meetings, and websites visited for research. Despite encryption and local storage, the new feature raises privacy concerns for certain Windows users.
"Recall uses Copilot+ PC advanced processing capabilities to take images of your active screen every few seconds," Microsoft says on its website. "The snapshots are encrypted and saved on your PC’s hard drive. You can use Recall to locate the content you have viewed on your PC using search or on a timeline bar that allows you to scroll through your snapshots."
By performing a Recall action, users can access a snapshot from a specific time period, providing context for the event or moment they are searching for. It also allows users to search through teleconference meetings they've participated in and videos watched using an AI-powered feature that transcribes and translates speech.

Microsoft's Surface Pro 11 comes with Arm chips and an optional OLED display panel. [credit: Microsoft ]
If at first you don't succeed, try, try again.
Microsoft has announced a pair of new devices powered by Qualcomm's Snapdragon X Plus and X Elite processors. They're far from Microsoft's first PCs with Arm processors in them—2012's original Surface, the Surface Pro X, and the Surface Pro 9 with 5G have all shipped with Arm's chips instead of Intel's or AMD's. But today's new Surface Pro and Surface Laptop are the first Arm devices to be the primary Surface offerings rather than a side offering, and they're the first to credibly claim that they can both outperform comparable Intel- and AMD-designed chips while offering better battery life, a la Apple's M1 chip in 2020.
One caveat that I hadn't seen mentioned in Microsoft's presentation or in other coverage of the announcement, though: Microsoft says that both of these devices have fans. Apple still uses fans for the MacBook Pro lineup, but the MacBook Air is totally fanless. Bear that in mind when reading Microsoft's claims about performance.
Read more of this story at Slashdot.
Read more of this story at Slashdot.
Google is invoking the 'monoculture' word in response to a scathing U.S. government report on Microsoft's inadequate cybersecurity practices.
The post Google Cites ‘Monoculture’ Risks in Response to CSRB Report on Microsoft appeared first on SecurityWeek.

Enlarge (credit: Microsoft)
Microsoft is using its new Surface launch and this week’s Build developer conference as a platform to launch its new “Copilot+" PC initiative, which comes with specific hardware requirements that systems will need to meet to be eligible. Copilot+ PCs will be able to handle some AI-accelerated workloads like chatbots and image generation locally instead of relying on the cloud, but new hardware will generally be required to run these workloads quickly and power efficiently.
At a minimum, systems will need 16GB of RAM and 256GB of storage, to accommodate both the memory requirements and the on-disk storage requirements needed for things like large language models (LLMs; even so-called “small language models” like Microsoft’s Phi-3, still use several billion parameters). Microsoft says that all of the Snapdragon X Plus and Elite-powered PCs being announced today will come with the Copilot+ features pre-installed, and that they'll begin shipping on June 18th.
But the biggest new requirement, and the blocker for virtually every Windows PC in use today, will be for an integrated neural processing unit, or NPU. Microsoft requires an NPU with performance rated at 40 trillion operations per second (TOPS), a high-level performance figure that Microsoft, Qualcomm, Apple, and others use for NPU performance comparisons. Right now, that requirement can only be met by a single chip in the Windows PC ecosystem, one that isn't even quite available yet: Qualcomm's Snapdragon X Elite and X Plus, launching in the new Surface and a number of PCs from the likes of Dell, Lenovo, HP, Asus, Acer, and other major PC OEMs in the next couple of months. All of those chips have NPUs capable of 45 TOPS, just a shade more than Microsoft's minimum requirement.

Enlarge / A PC running Windows 11. (credit: Microsoft)
Microsoft is going all-in on Arm-powered Windows PCs today with the introduction of a Snapdragon X Elite-powered Surface Pro convertible and Surface Laptop, and there are inevitable comparisons to draw with another big company that recently shifted from Intel’s processors to Arm-based designs: Apple.
A huge part of the Apple Silicon transition’s success was Rosetta 2, a translation layer that makes it relatively seamless to run most Intel Mac apps on an Apple Silicon Mac with no extra effort required from the user or the app’s developer. Windows 11 has similar translation capabilities, and with the Windows 11 24H2 update, that app translation technology is getting a name: Prism.
Microsoft says that Prism isn’t just a new name for the same old translation technology. Translated apps should run between 10 and 20 percent faster on the same Arm hardware after installing the Windows 11 24H2 update, offering some trickle-down benefits that users of the handful of Arm-based Windows 11 PCs should notice even if they don’t shell out for new hardware. The company says that Prism's performance should be similar to Rosetta's, though obviously this depends on the speed of the hardware you're running it on.
News avatars are proliferating on social media and experts say they will spread as the technology becomes more accessible
The news presenter has a deeply uncanny air as he delivers a partisan and pejorative message in Mandarin: Taiwan’s outgoing president, Tsai Ing-wen, is as effective as limp spinach, her period in office beset by economic under performance, social problems and protests.
“Water spinach looks at water spinach. Turns out that water spinach isn’t just a name,” says the presenter, in an extended metaphor about Tsai being “Hollow Tsai” – a pun related to the Mandarin word for water spinach.
Continue reading...© Photograph: Storm-1376
© Photograph: Storm-1376
Microsoft is working on a promising-looking protocol to lock down DNS.
ZTDNS aims to solve this decades-old problem by integrating the Windows DNS engine with the Windows Filtering Platform—the core component of the Windows Firewall—directly into client devices.
Jake Williams, VP of research and development at consultancy Hunter Strategy, said the union of these previously disparate engines would allow updates to be made to the Windows firewall on a per-domain name basis. The result, he said, is a mechanism that allows organizations to, in essence, tell clients “only use our DNS server, that uses TLS, and will only resolve certain domains.” Microsoft calls this DNS server or servers the “protective DNS server.”...
The post Zero-Trust DNS appeared first on Security Boulevard.
Microsoft is working on a promising-looking protocol to lock down DNS.
ZTDNS aims to solve this decades-old problem by integrating the Windows DNS engine with the Windows Filtering Platform—the core component of the Windows Firewall—directly into client devices.
Jake Williams, VP of research and development at consultancy Hunter Strategy, said the union of these previously disparate engines would allow updates to be made to the Windows firewall on a per-domain name basis. The result, he said, is a mechanism that allows organizations to, in essence, tell clients “only use our DNS server, that uses TLS, and will only resolve certain domains.” Microsoft calls this DNS server or servers the “protective DNS server.”
By default, the firewall will deny resolutions to all domains except those enumerated in allow lists. A separate allow list will contain IP address subnets that clients need to run authorized software. Key to making this work at scale inside an organization with rapidly changing needs. Networking security expert Royce Williams (no relation to Jake Williams) called this a “sort of a bidirectional API for the firewall layer, so you can both trigger firewall actions (by input *to* the firewall), and trigger external actions based on firewall state (output *from* the firewall). So instead of having to reinvent the firewall wheel if you are an AV vendor or whatever, you just hook into WFP.”
Patch Tuesday: Microsoft documents 60 security flaws in multiple software products and flags an actively exploited Windows zero-day for urgent attention.
The post Microsoft Warns of Active Zero-Day Exploitation, Patches 60 Windows Vulnerabilities appeared first on SecurityWeek.

A study analyzing Apple, Microsoft, and SpaceX suggests that return to office (RTO) mandates can lead to a higher rate of employees, especially senior-level ones, leaving the company, often to work at competitors.
The study (PDF), published this month by University of Chicago and University of Michigan researchers and reported by The Washington Post on Sunday, says:
In this paper, we provide causal evidence that RTO mandates at three large tech companies—Microsoft, SpaceX, and Apple—had a negative effect on the tenure and seniority of their respective workforce. In particular, we find the strongest negative effects at the top of the respective distributions, implying a more pronounced exodus of relatively senior personnel.
The study looked at résumé data from People Data Labs and used "260 million résumés matched to company data." It only examined three companies, but the report's authors noted that Apple, Microsoft, and SpaceX represent 30 percent of the tech industry's revenue and over 2 percent of the technology industry's workforce. The three companies have also been influential in setting RTO standards beyond their own companies. Robert Ployhart, a professor of business administration and management at the University of South Carolina and scholar at the Academy of Management, told the Post that despite the study being limited to three companies, its conclusions are a broader reflection of the effects of RTO policies in the US.

Enlarge (credit: Microsoft)
Brussels is set to issue new antitrust charges against Microsoft over concerns that the software giant is undermining rivals to its videoconferencing app Teams.
According to three people with knowledge of the move, the European Commission is pressing ahead with a formal charge sheet against the world’s most valuable listed tech company over concerns it is restricting competition in the sector.
Microsoft last month offered concessions as it sought to avoid regulatory action, including extending a plan to unbundle Teams from other software such as Office, not just in Europe but across the world.
Microsoft is making security its number one priority for every employee, following years of security issues and mounting criticisms. After a scathing report from the US Cyber Safety Review Board recently concluded that “Microsoft’s security culture was inadequate and requires an overhaul,” it’s doing just that by outlining a set of security principles and goals that are tied to compensation packages for Microsoft’s senior leadership team.
↫ Tom Warren at The Verge
The devil is in the details regarding tying executive pay to security performance, but it we take it at face value and assume good intent – which is a laughable assumption in our corporatist world, but alas – I would like to see more of this. It’s high time executives start paying – literally and figuratively – for the failings of the companies and teams they claim to run.
Microsoft security chief Charlie Bell pledges significant reforms and a strategic shift to prioritize security above all other product features.
The post Microsoft Overhauls Cybersecurity Strategy After Scathing CSRB Report appeared first on SecurityWeek.
Years of accumulated security debt at Microsoft are seemingly crashing down upon the company in a manner that many critics warned about, but few ever believed would actually come to light.
Microsoft is an entrenched enterprise provider, owning nearly one-quarter of the global cloud infrastructure services market and, as of Q1 last year, nearly 20% of the worldwide SaaS application market, according to Synergy Research Group.
Though not immune to scandal, in the wake of two major nation-state breaches of its core enterprise platforms, Microsoft is facing one of its most serious reputational crises.
↫ David Jones at Cybersecurity Dive
It’s almost like having the entire US government dependent on a single vendor is a bad idea.
Just spitballing here.
Microsoft provides an easy and logical first step into GenAI for many organizations, but beware of the pitfalls.
The post Why Using Microsoft Copilot Could Amplify Existing Data Quality and Privacy Issues appeared first on SecurityWeek.
Regarding the release of the MS-DOS 4.00 source code, Michal Necasek makes an excellent point about how just dumping the code in git is a terrible and destructive way to release older source code.
It’s terrific that the source code for DOS 4.00/4.01 was released! But don’t expect to build the source code mutilated by git without problems.
Historic source code should be released simply as an archive of files, ZIP or tar or 7z or whatever, with all timestamps preserved and every single byte kept the way it was. Git is simply not a suitable tool for this.
↫ Michal Necasek at OS/2 Museum
The problems caused by dumping the code in git are quite real. Timestamps are not preserved, and the conversion to UTF-8 is deeply destructive, turning some parts of the code to literal gibberish. It’s a bit of a mess, and the people responsible for these release should be more careful and considerate.